ISO 27001
ISO 27001:2022 Transition Strategy
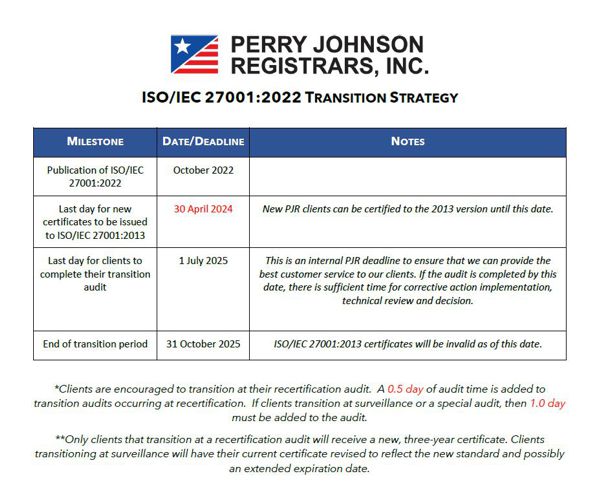
Are you ready for the transition to the new version of ISO 27001? Check out this table of important dates and keep an eye out for upcoming webinars on the topic of successfully transitioning to ISO 27001:2022!
 |
Now Available: ISO 27001:2022
ISO 27001:2022 is here! The newest revision of the ISO 27001 standard has been released as of October 2022, and the PDF of the standard is available for purchase on the ISO website. While details regarding transition timelines have yet to be determined, here is some Q&A on important points that you should know:
Q: What is changing?
A: Fortunately, most of the changes to the standard are related to its structure and layout. The majority of controls will remain in place, with only minor alterations to Annex A. Other planned changes will include subtle changes around wording: Identity and Authentication Management will replace “password management,” User End Point Devices will not be used instead of “Mobile Devices,” and Asset Management” will now include an inventory of information. Due to the emergence of new vulnerabilities and technologies since the release of the 2013 standard, new controls will also be added, and include the introduction of hashtags (#) next to each control, in order to help you understand what elements or functions the control perform within the ISMS. (#preventative, #detective, #corrective).
Q: What will I need to re-certify to the new version?
A: Clients will have ample opportunity to transition, with a transition period lasting until October 31, 2025. During this transition period, you will be able to update your ISMS with new controls, implement changes, and record training activities as appropriate. Then PJR will conduct a recertification audit against the new standard and issue a new certificate.
Q: What if I am new to certification?
A: If you are working toward ISO 27001 certification for the first time, you will be allowed to choose which version you certify to, then need to make the transition within the time allotted; new certifications to the 2013 version of the standard will be allowed through April 30, 2024. After that date only audits to ISO 27001:2022 will be conducted.
Q: Where can I find more information?
A: PJR will continue to update our website as more information becomes available, so be sure to check back regularly for additional changes!
Your Journey to ISO 27001 (video) Series
ISO 27001 is the international standard for Information Security Management Systems (ISMS). It provides a model for risk assessment, security design and implementation, and security management. The ISO 27001 standard specifies implementation and management guidelines to help keep your information safe.
ISO 27001 is the only international auditable standard for Information Security Management Systems. It provides independent assurance that your organization complies with legal, statutory, regulatory, and contractual requirements bearing sensitive information. Obtaining an ISO 27001 certification proves that you have taken necessary steps to protect sensitive information against unauthorized access.
Who needs ISO 27001?
Any organization that holds sensitive information is a candidate for ISO 27001 certification. In particular, companies in the healthcare, finance, public, and IT sectors can benefit greatly from a certified ISMS.
More Information on ISO 27001:
- ISO 27002: How Is It Different From 27001 And What’s New?
- What is ISO 27001?
- Key Components of ISO 27001
- Cyber Security for Electronic Medical Devices
- What is an Information Security Management System?
- How ISO 27001 Provides Cyber Security for the Banking Industry?
- How ISO 27001 Can Protect Medical Organizations from Cyber Threats
- Overview of Certification
- List of mandatory documents required by ISO 27001 (2013 revision)
For more information on ISO 27001, contact PJR today at (248) 358-3388 or send a request to [email protected] for a Project Manager in your area!

(248) 358-3388
Call PJR Today!